While looking into the new Microsoft Defender Antivirus report available in MEM (Intune) I discovered some machines which did not report any recent Defender antimalware scans, despite configured via configuration profile. Of course, AV scans are kinda old-fashioned against rapidly evolving threats but a regular quick scan won’t hurt anyone. Instead of having a look at every single machine affected, I decided to try out the new proactive remediations feature which went globally available last week and let endpoint analytics do the detection and remediation work for me. As a reference, I used the Tutorial: Proactive remediations from Microsoft which covers the process quite well.
PowerShell scrips#
For Endpoint analytics / Proactive remediations we need two PowerShell scripts. The first script is used as a detection script and determines whether remediation is necessary based on the exit code. Exit code 0 indicates a healthy status and exit code 1 indicates remediation necessary. Remediation occurs with a second PowerShell script.
To detect the most recent Defender scan I used the Windows Eventlog. Event ID’s are documented here.
Detection script#
Remediation script#
The remediation script is just about a one-liner to trigger a quick scan. You can extend this based on your requirements and respective to your Intune settings. E.g. triggering a signature update for a scan or adding additional steps.
Create a new proactive remediations script package#
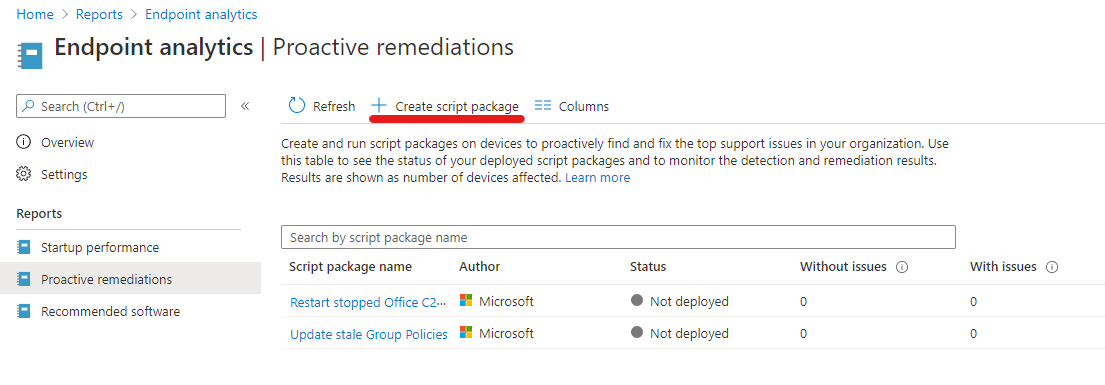
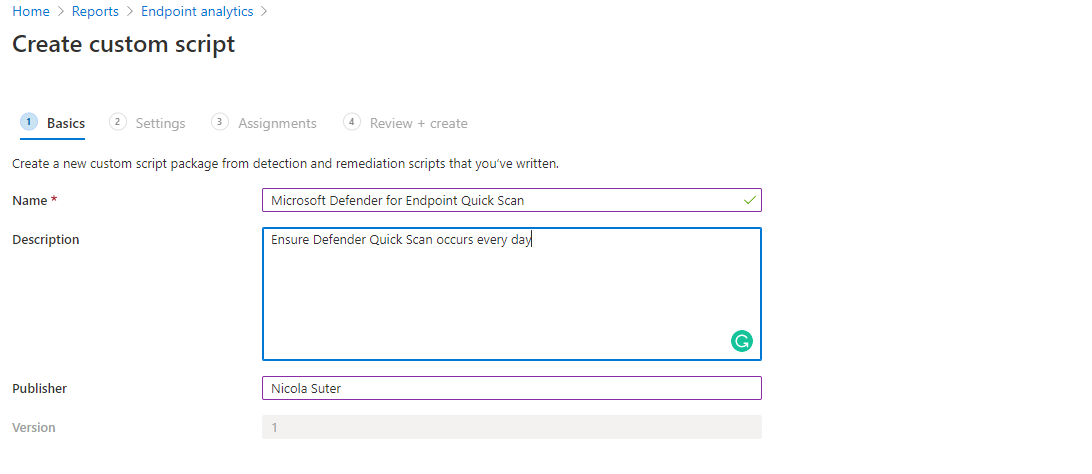
Adding a new proactive remediation script package is fairly easy. We simply need to upload the detections and remediation script and target the package to an AAD group and specify a schedule. You can find the Endpoint analytics | Proactive remediations section in your tenant under the “Reports” blade.
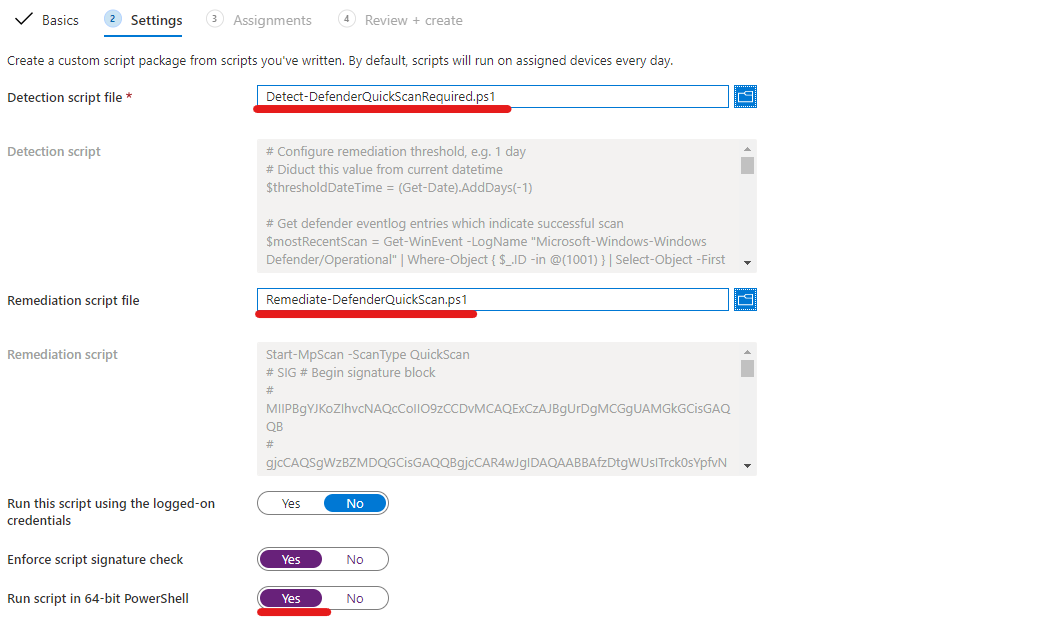
Add the detection and remediation script, I encourage you to sign those and enforce script signature check (only succeeds if signed) although this is optional
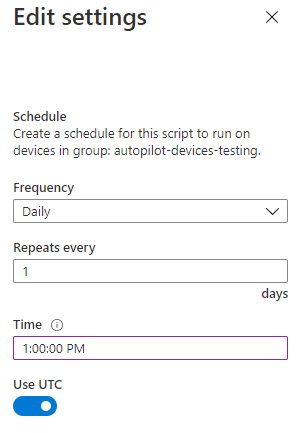
Assign the remediation package & click on edit to modify the schedule
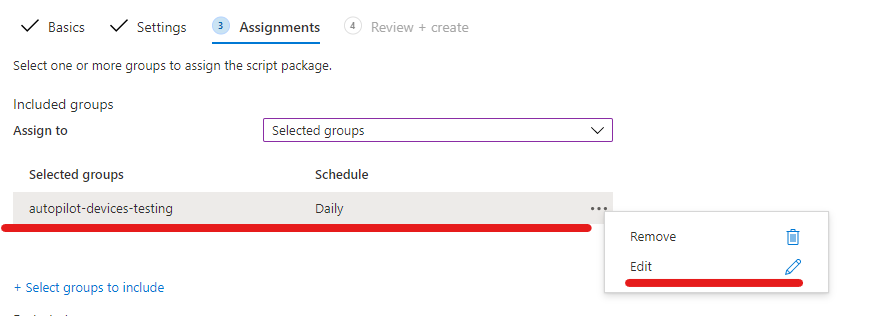
Specify your desired schedule
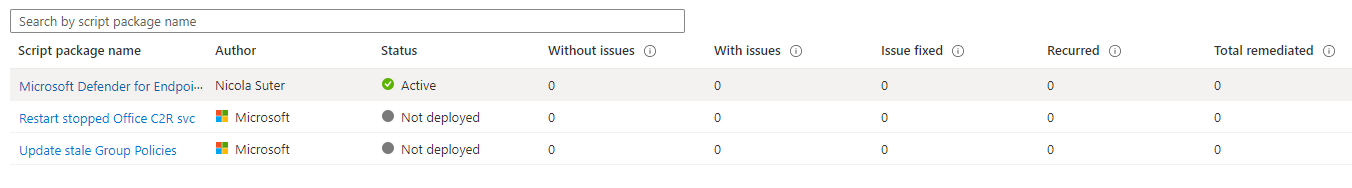
Afterwards, you can see the script package and track the status of the package:
Final words#
I hope this remediation package helps you to ensure quick scans running smoothly in your Microsoft Endpoint Manager environment and provides you an idea about the future possibilities with the new endpoint analytics / proactive remediations feature. Did you also find some clients not doing the quick scans regularly? Let me know in the comments section.