If you imagine that your users or administrators have uncontrolled local administrator rights it’s a nightmare. They have (certainly) full control over their computer, and could do a lot of harm. So managing local administrator rights is definitely a must.
Manage Local Administrator Rights#
The Active Directory Group Policies offer a great possibility to manage local groups on clients or servers. All the magic happens with “Restricted Groups”.
Adding a group or users to a local group#
If you want to add a certain group to a built-in group add the group to the restricted groups under the “This group is a member of” sections: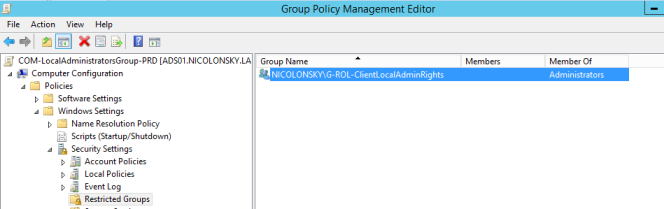
When the GPO is no longer applied, the restricted group is being removed from the clients.
Overwrite local group members#
When you wan’t take full control over a local group, you can choose the “Members of this group” option. Then all group members are replaced with the specified users or groups here, except the built-in local Administrator account.
==Caution: Be careful overwriting the local Administrators group because you don’t want to lock out yourself, do you?==
So I would recommend to add at least the “Domain Admins” to the members: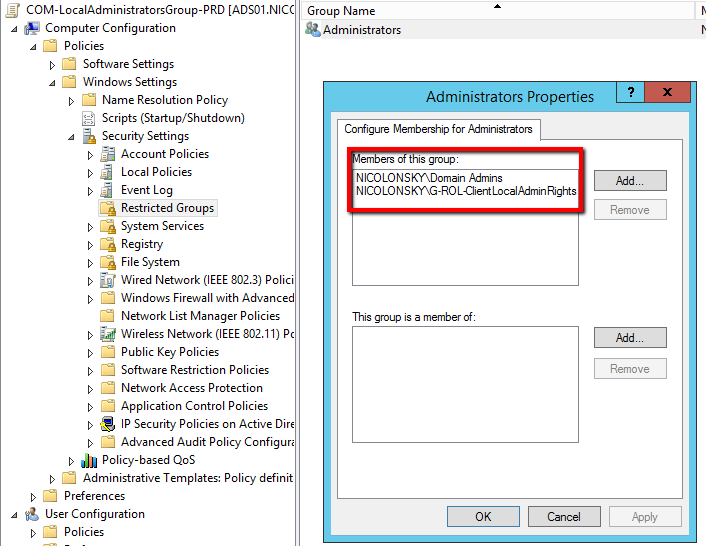
Choosing the right option#
The only but important difference between this two options is:
With the explicit declaration for the members the group gets overwritten with each policy refresh - you won’t have any unwanted users or groups in your local Administrators group.
Resulting client settings#
Last but not least with both options we achieve the following configuration for the local Administrators group on a client: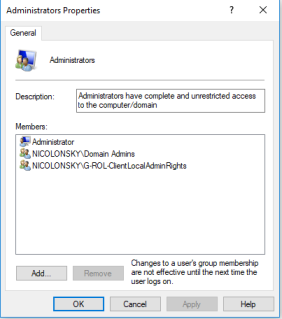
Conclusion#
Restricted Groups offer a great possibility to manage the local user rights in your environment. Combined with the Local Administrator Password Solution it’s a big step towards a secure and more maintainable solution.
Reference:
